Software development process has become more complex in the current predicament with several remote and on-site teams working together. So, you need to have a security mechanism in place to ensure data protection across the software development lifecycle.
But why?
It’s simple if you don’t invest in the security of the system development life cycle, the total cost of ownership will rise-
HOW?
The global data breach cost is $4.45 million, growing by 15% annually. So if you are not planning for secure software development, you may end up paying more than the budget. But, how to cope with the security requirements of the software development process.
A simple answer is to have a software development life cycle (SDLC) security requirements checklist. Leveraging an SDLC security checklist you can ensure better data and system protection against cyberattacks throughout the lifecycle.
This article will help you understand the software development life cycle and provide a comprehensive sdlc security requirements checklist. Let’s first understand SSDLC for your project.

What is the Secure Software Development Life Cycle (SSDLC)?
Secure Software Development Life Cycle(SSDLC) is a security framework that provides a structure for data protection across the software development process. Securing the SDLC includes adding a security testing process at each stage of the software development lifecycle.
Right from the design stage to development and deployment, software development life cycle security ensures security for the entire process. It involves requirement gathering, need analysis, architecture design for secure operations, and implementing extensive software testing.
SSLDC follows an iterative process of different phases, including security requirements, design, development, testing, deployment, and maintenance. It adopts security controls to protect the life cycle by creating secure software.
The main purpose of using SSLDC methodology is to confirm the presence of essential components in the software environment is secure. It also helps reduce the costs caused by design flaws and vulnerabilities and offers long-term viability to the project
But is SSDLC worth investing in?
Here are some key reasons!
Why Is SDLC Important: 6 Benefits of SDLC
Software Development Life Cycle (SDLC) is an ongoing process. Your project activities do not end as you launch software, so it is also crucial to plan for security at each stage of SDLC.
Some of the key reasons SDLC matters for any organization why and security integration is so important are:
1. Structured Approach
Software development is a complex process where multiple phases occur and if you don’t use a structured approach, it can lead to errors. Take an example of the software development process, which requires not just effective coding practices but effective testing and incremental improvements.
While many organizations have a siloed approach to software development. A structured and collaborative SDLC can offer high-quality software delivery.
2. Quality Assurance:
Ensuring software quality does not mean focusing only on the design or development aspects. It’s a continuous process where you must keep testing your software and ensure better quality with each iteration.
Continuously improving the software quality and ensuring better performance encapsulated different stages of software development life cycle security. Without effective quality assurance activities across SDLC, your software quality will take a hit.
3. Risk Management
SDLC helps you detect the errors early and reduce the risks of cyberattacks. Integrating the testing across SDLC stages helps in improving the performance and quality of your software. Take an example of the testing in production approach where you can test directly within the live production environment rather than in a separate testing environment.
If you want to use the testing in-production approach SDLC methodology becomes crucial because the production environment is available for testing only after you launch the software. However with the conventional approach of focusing only upto the deployment of software does not allow you to test within a production environment, increasing the risks of errors that go unnoticed during the development phase.
4. Cost-Effectiveness
The software development life cycle approach helps reduce repeated errors, leading to lower operational costs. For example, if you test the software for failure, you can detect errors earlier, which can cause massive disruptions later on in the production environment.
Using SDLC improves the development speeds and minimizes risks related to the project, reducing the cost of production. Further integrating security testing across the phases of software development, SDLC helps reduce the costs of error detection and resolution through early failure remediation.
5. Customer Satisfaction
SDLC helps improve the quality of software, which in turn improves customer satisfaction. Another important aspect of using software development life cycle is improved system security.
Due to testing at each stage of software development, deployment, and production environments, risks are minimized, leading to higher security for user data.
This allows businesses to better comply with leading data regulations like GDPR and PCI DSS. Better compliance with data regulations and security improves user trust and customer satisfaction.
6. Scalability and Maintenance
The software development life cycle approach allows you to improve scalability and maintenance differently.
For example, SDLC offers a systematic management framework for increased visibility of the development process, efficient cost estimation, planning, and scheduling.
SDLC also helps facilitate efficient maintenance by offering a systematic approach to delivering software that meets customer demands.
Understanding the importance of SDLC, you now know why it is so popular among organizations. However, what’s crucial is to understand all the stages to prepare for security integrations.
The 6 Stages Of A Software Development Life Cycle
From gathering the project requirements to deploying and maintaining the software, there are six stages of SDLC encapsulating several important aspects.
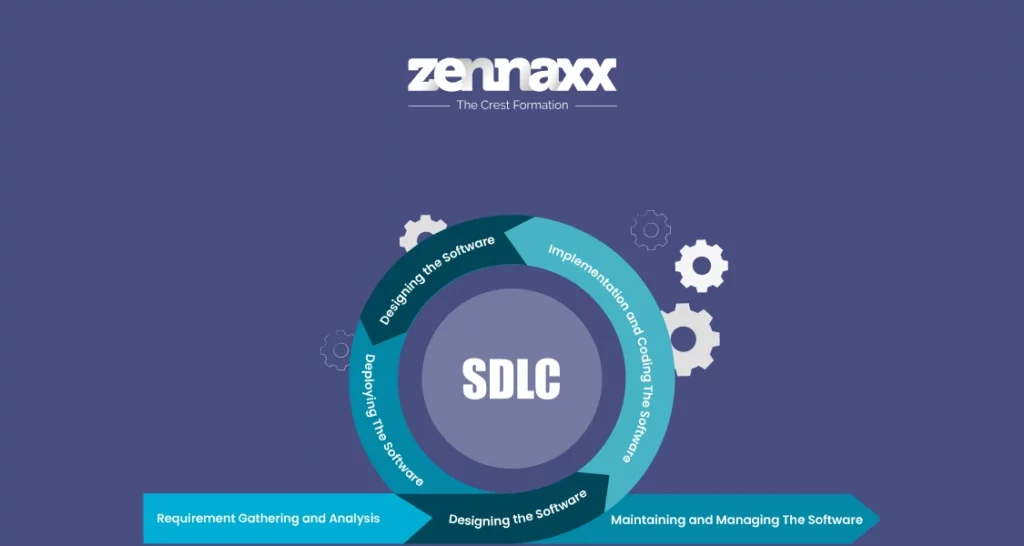
Stage 1: Requirement Gathering and Analysis
During the first phase of SDLC, the main objective is to understand the software product’s requirements clearly.
This involves conducting a thorough analysis of the business needs, consulting with all stakeholders, and gathering all necessary information to define a comprehensive specification.
Plan the project by dividing work, setting milestones, creating timelines, getting cost estimates, conducting risk analysis, and devising a mitigation plan, using the “Software Requirements Specification” as a reference. Focus on delivering high-quality work on time and within budget.
Stage 2: Designing the Software
In the software development process, the second phase involves creating the software architecture with the SRS (Software Requirements Specification) as the reference.
This phase focuses on two key aspects: High-Level Design (HLD) and Low-Level Design (LLD). In HLD, the software’s overall structure, components, modules, architecture, and relationships between them are outlined, while LLD provides the actual implementation details.
The design phase ensures that the software meets the defined requirements and involves multiple stakeholders, including designers and architects. There are two key elements of the software design that you will create during this phase:
● Software architecture, which provides a process flow and structure for different elements in a code.
● Design prototype or wireframe developed by the UI/UX team providing an overview for the users or clients
Stage 3: Implementation and Coding The Software
In the Implementation and Coding stage of SDLC, the software is created based on approved design. Code is written, tested, and integrated. Collaboration is crucial to ensure the software meets specs. DevOps can improve software quality through better collaborations. The design prototype provides an overview for clients.
Stage 4: Testing the Software
Testing the software is a stage where you ensure that the digital product achieves the desired outcome, This includes testing it for functionality, usability, accessibility, and compatibility across platforms.
You also need to test the software for backward compatibility ensuring access across older and newer devices.
This is where regressive software testing becomes essential for your project. Apart from the regressive testing you also need to test the software for security purposes ensuring better data protection.
Stage 5: Deploying The Software
Deployment phase involves making the software live and functional in the production environment. Testing in the product environment is crucial for enhanced performance.
Embrace DevOps culture for improved collaborations, reduced errors, and faster deployment. Continuous integration and delivery are key for improving software quality with each deployment iteration.
Stage 6: Maintaining and Managing The Software
This stage is an ongoing process that continues throughout the SDLC. It involves all activities necessary to keep the software running smoothly and efficiently, including:
- Bug fixing: Resolving any errors or defects in the software.
- Security patching: Updating the software to address security vulnerabilities.
- Performance tuning: Optimizing the software to improve its speed and responsiveness.
- Change management: Managing changes to the software, such as new features or enhancements.
- Documentation updates: Keeping the software documentation up-to-date.
- Support: Providing technical support to users who experience problems with the software.
Now that you know how different stages of SDLC are, it’s time to understand the security integration requirements.
Worried about security gaps in your software development lifecycle?
Let’s fortify your processes from start to finish. Ready to strengthen your defenses?
Overview of the SDLC Phases and Security Considerations in Each SDLC Phase
Securing software development is crucial to protect applications and data from cyber threats. It involves implementing security measures throughout the development life cycle, adhering to secure coding guidelines, identifying and assessing potential threats to a software system, and implementing counter measures to mitigate risks through threat modeling.
Phase 1: Requirements Gathering
Security considerations are essential in requirements gathering because they help to ensure that the system being developed is protected from unauthorized data access. Identifying security requirements and conducting risk assessments, organizations can develop systems that are more secure.
Identifying security requirements
Security requirements are the specific measures that must be taken to protect a system from unauthorized access, use, disclosure, disruption, modification, or destruction. These requirements can be identified through a variety of methods, including
- Interviews with stakeholders can provide valuable input on the security risks that are most relevant to the system being developed.
- Risk assessments can help to identify the potential threats to the system and the likelihood and impact of each threat.
- Review of existing security policies can provide guidance on the security requirements that should be implemented.
Conducting risk assessments
The goal of a risk assessment activity is to determine the impact of each risk and develop strategies to mitigate them. Risk assessments can be conducted using a variety of methods, including
- Qualitative risk assessment helps estimate the likelihood and impact of each risk by using specific judgements
- Quantitative risk assessment uses data and analysis to determine the impact of each risk.
The output of a risk assessment is a risk register, which lists the identified risks, their likelihood and impact, and the strategies that will be used to mitigate those risks.
Phase 2: Architecture and Design
When developing a software system, it is essential to consider the security objectives of the system, including confidentiality, integrity, availability, and non-repudiation. Specific security requirements should be defined to mitigate these risks and protect the system.
Identifying Security Requirements
To ensure a secure software system, develop a security architecture with defined responsibilities, policies, and procedures. Integrate security controls like authentication, authorization, encryption, and logging.
Implement security measures at various system levels and properly configure and test security controls for effective protection.
Defining Security Controls
To create secure software systems, architects and designers must identify threats, select and implement specific security controls, implement secure coding practices, conduct security testing and monitoring, and develop an incident response plan.
By following these considerations, they can create software that meets the organization’s security requirements and protects against evolving threats and vulnerabilities.
Phase 3: Implementation
The SDLC implementation phase is where software is built. This phase involves converting the design specifications into an actual working system. It is crucial to integrate security measures during this phase to ensure integrity.
Secure Coding Practices and Guidelines
It is important to establish and enforce secure coding standards and guidelines that developers can follow to ensure the security of software applications.
This includes using secure coding tools and techniques to prevent common vulnerabilities like buffer overflows, SQL injections, and cross-site scripting.
Regular code reviews must also be conducted to recognize and address potential security issues before they become a problem.
Input Validation and Data Sanitization
Input validation ensures that whatever data the user provides conforms to the expected format and falls within acceptable ranges. It is crucial to sanitize user inputs to eliminate any malicious characters or code that could exploit vulnerabilities.
One way to streamline the process and minimize errors is to use input validation libraries or frameworks. Further, you can leverage the following tips:
- Establish clear rules and criteria for validating user input.
- Implement validation checks in the application code to verify that user input meets the defined rules. Thoroughly test the input validation mechanisms to ensure they are working as intended
- Periodically review and update the input validation rules
- Determine which data fields contain sensitive information that needs to be sanitized.
- Replace sensitive data with unique identifiers that can be used to retrieve the original data.
- Encrypt sensitive data using a cryptographic algorithm to make it unreadable for hackers.
- Apply the chosen sanitization method to the identified sensitive data.
- Test the sanitized data to confirm that it has been effectively removed
Access Control Mechanisms
To ensure the security of your system resources and data, it’s essential to implement access control mechanisms. You can achieve this by defining data access permissions based on the principle of least privilege.
Use authentication and authorization techniques to verify user identities and grant appropriate access. In addition to this, there are some other security considerations to keep in mind.
- Conduct threat modeling to identify potential security risks and develop mitigation strategies.
- Perform security testing to identify and address vulnerabilities before deployment.
- Establish configuration management processes to apply security settings across the system.
- Develop an incident response plan to outline procedures for responding to and recovering.
Phase 4: Testing
The Testing phase of SDLC is a continuous process as you will be conducting tests throughout the software development, deployment,and even after the release. So, you need to plan the entire testing phase and define key security integrations.
Security testing methodologies
Security testing is a process of conducting specific tests on your software to evaluate its resilience to cyberattacks. This includes doing manual code reviews and dynamic and static analysis.
Manual Code Review
Manual code review involves thoroughly examining the source code by reviewers to identify security vulnerabilities, coding errors, and best practices adherence.
Reviewers analyze the code line by line, looking for potential security flaws such as validation issues, insecure data storage, or improper error handling.
Manual code review can uncover complex security issues that automated tools may overlook and is essential for assessing the overall security posture of the codebase.
Dynamic Analysis
Dynamic analysis, also known as black-box testing, involves analyzing the software in operation. It assesses the code’s behavior regarding inputs, outputs, and overall performance under different conditions.
Unlike static analysis, dynamic analysis does not examine the source code but focuses on identifying vulnerabilities and potential security issues while the software runs.
Static Analysis
Static analysis, also known as white-box testing, involves the examination of the source code or binary code without executing the program. It aims to identify security vulnerabilities, coding errors, and adherence to coding standards.
By leveraging specialized tools, static analysis can identify potential vulnerabilities such as buffer overflows, injection attacks, and other common security issues.
This methodology is effective at detecting security flaws early in the development process and is crucial for ensuring the overall security robustness of the software.
Vulnerability scanning and penetration testing
Adding vulnerability scanning and penetration testing to your software testing phase in SDLC helps ensure the security of your systems. These vulnerabilities can attract cybercrimes, costing up to $10.5 trillion by 2025. Vulnerability scanning identifies and assesses weaknesses in a network.
Vulnerability scanners typically compare configuration and versions of a software to a database of known vulnerabilities.d
Penetration testing helps identify vulnerabilities that an attacker could exploit. Penetration testers simulate an attempt to gain access to the system or network and escalate privileges.
Phase 5: Deployment
The deployment phase of SDLC deals with the release of the software leveraging an iterative process. However ensuring secure software development needs security integrations in the deployment phase also. This is a crucial aspect of your SDLC security requirements checklist.
Security testing methodologies
There are various security testing methodologies, each with its own strengths and weaknesses. Some of the most common methodologies include:
- Static Application Security Testing (SAST) is a security testing where you analyze the source code of an application to identify potential vulnerabilities..
- Dynamic Application Security Testing (DAST) is a testing approach where you analyze the behavior of an application while it is running.
- Security Audits: Security audits are a type of security testing that involves a comprehensive review of a system’s security controls and procedures.
Secure Deployment Practices
Secure deployment practicesare the measures taken to ensure that software applications are deployed in a secure environment that can withstand unauthorized access, data breaches, and other security threats.
Some common secure deployment practices include
- Use a secure deployment pipeline to deploy software applications.
- Use secure deployment tools to help you deploy software applications securely. These tools can automate security checks, scan for vulnerabilities, and enforce security policies.
- Train your team on secure deployment practices so that they can help to ensure the security of your deployments.
Phase 6: Maintenance and Support
Maintenance and support stage of your SDLC project deals with the activities of monitoring the software, and fine-tuning performance with technical support functions.
A key aspect of the maintenance stage that you need to incorporate in your SDLC checklist is DevSecOps integration.
You need to establish a cross-functional DevSecOps team that includes developers, security engineers, and operations staff. This team will be responsible for developing and implementing your DevSecOps strategy, which includes critical maintenance and support activities.
For example, security patches are an essential activity for risk management in software development.
Patch management
Security patch management involves regularly updating the software with code patches and securing it against the latest cyber threats. This is crucial for both newer versions and older versions. So, you also need to plan for patch management to accommodate backward compatibility.
Incident response and monitoring
Incident response involves identifying and responding to security incidents, assessing their impact, and mitigating the damage.
It continuously keeps an eye on a system for security incidents using various tools. Incident response and monitoring are vital for safeguarding an organization from security threats.
You can use security information event management (SIEM) systems, intrusion detection systems (IDS), and log analysis for continuous monitoring and ensure better incident responses.
While this SDLC checklist looks comprehensive, the compliance and regulatory requirements for secure development demand the implementation of specific best practices.
Such secure SDLC best practices include having clear requirements, maintaining a growth mindset, and most importantly training your team for security practices.
5 Secure SDLC Best Practices
To ensure a secure SDLC, prioritize security throughout the development process. This may require a cultural shift and the implementation of automated processes, workshops, and code reviews.
However, each organization may require a unique approach due to differences in software development team strengths and weaknesses.
1. Educate Your Developers
Educating developers is a crucial part of your SDLC checklist because it helps you reduce human errors and related security issues. You can train your developers by,
- Having standard guidelines that include secure coding practices
- Creating security training modules for developers
- Defining specific security policies and ensuring compliance
2. Have Clear Requirements
From secure architecture design principles to specific testing tools every requirement of your project needs to be defined well.
A lack of understanding of the requirements can lead to security issues. So it is important that you gather all the information right before you begin the SDLC.
3. Maintain a Growth Mindset
Cross-functional teams are one of the major aspects of any SDLC process and this is why your teams need to have a growth mindset. Without a proper growth mindset and an open mind, it will affect the DevOps culture of the organization.
4. Tie Implementation to Other Initiatives
If you are just focusing on software development life cycle security, the chances are the results may be tricky to achieve. However, if you tie it to another initiative like implementing DevSecOps integration or cloud migration, results can be better.
Especially if you use CI/CD best practices with SSLDC your systems will have maximum potential and higher security.
5. Tackle the Big Problems First
While you are planning your SDLC checklist the focus needs to be on the biggest security risks that the system is facing. Focusing on each vulnerability may not be practical each time.
The best approach is to plan your SSLDC for major security threats and while your software is in production focus on testing and reducing vulnerabilities.
Want to Automate Your Business Process With a Software Solution?
Zennaxx, a leading software development firm in Canada, has delivered 700+ bespoke solutions spanning various industries.
Frequently Asked Questions (FAQs)
- WHAT ARE THE BEST PRACTICES FOR ESTABLISHING A SECURITY-FOCUSED CULTURE DURING THE SDLC?
- Embedding security responsibilities throughout development, investing in security training, using secure development tools , and establishing clear security policies are all important steps to take. By implementing these best practices, you can ensure security throughout the development process and minimize the risk of data breaches.
- WHAT CHALLENGES MAY ARISE WHEN INTEGRATING SECURITY INTO THE SDLC, AND HOW CAN THEY BE ADDRESSED?
- Integrating security into the SDLC can pose several challenges, such as balancing security and agility, lack of security expertise, and resistance to change. To address these challenges, organizations can prioritize security requirements without hindering development progress through effective planning and collaboration. Investing in training and upskilling programs can also help enhance the security capabilities of development teams.
- HOW CAN ORGANIZATIONS STAY PROACTIVE IN ADDRESSING EVOLVING SECURITY THREATS THROUGHOUT THE SDLC?
- Employ threat intelligence monitoring, automated security testing, DevSecOps, and a threat-modeling mindset to bolster SDLC security. This approach identifies and resolves vulnerabilities early, minimizing security breach risks and assuring secure, reliable software.
- HOW CAN ORGANIZATIONS BALANCE SECURITY REQUIREMENTS WITH USABILITY CONCERNS DURING THE SDLC?
- Prioritize security without compromising usability by implementing measures that enhance protection. Involve users in the security design process to align features with their expectations.
- WHAT IS THE DIFFERENCE BETWEEN SDLC AND SSDLC?
- SDLC is a framework for developing software, while SSDLC is a specialized form that emphasizes security throughout the development phases. SSDLC includes security best practices, threat modeling, and secure coding techniques to create software with better security features and fewer vulnerabilities.
Conclusion
Increasing security threats and conventional approaches to testing for vulnerabilities are not sufficient. You need newer ways to secure software development.
Creating an SDLC checklist ensures security integrations throughout the development, deployment, and maintenance of software. software development life cycle security allows you to monitor risks, address security issues, and reduce vulnerabilities throughout the lifecycle.
Developing a comprehensive SDLC checklist, implementing best practices, and training your employees for it requires a reliable partner. This is where Zennaxx can help you with reliable SSDLC solutions for your project. Contact us now for more information.